PROCESSOR VULNERABILITY WORKAROUNDS
Back at the start of the year major chip manufacturers announced that two vulnerabilities would affect processors used in millions of devices. Codenamed ‘Meltdown’ and ‘Spectre’, these vulnerabilities left the door wide open for hackers to access user data that could be sensitive. The flaw, a result of a common design practice employed by most modern processors, has been publicly described as allowing an unprivileged attacker to bypass memory security restrictions and gain read access to privileged memory. Meaning that an unprivileged local attacker could be able to read privileged memory belonging to other processes or memory allocated to the kernel.
As promoted by Boston after the announcement, patches were quickly made available by major chip and OS vendors. A comprehensive list of solutions affected with associated patches issued by vendors can be found at https://www.supermicro.com/support/security_Intel-SA-00088.cfm
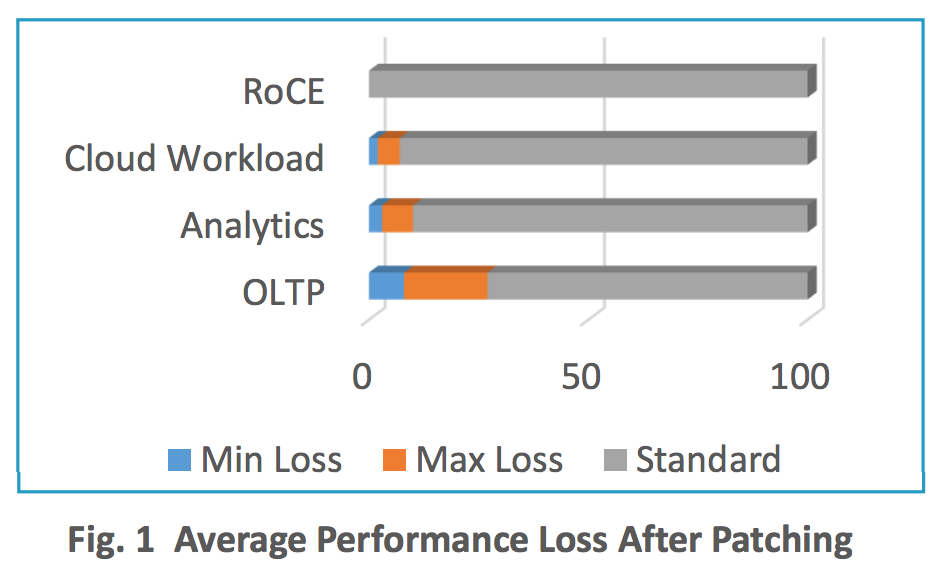
These patches have been found to have a knock-on effect on system performance – with some instances recorded up to -47% - those affected are strongly advised to evaluate the risk of patching versus the performance trade-off. So where does that leave organisations who cannot manage their applications with lower system performance?
Boston partners, Mellanox, a leading provider of high performance networking solutions, measured the impact on networking workloads. See before and after benchmark analysis results in figures 1-3.
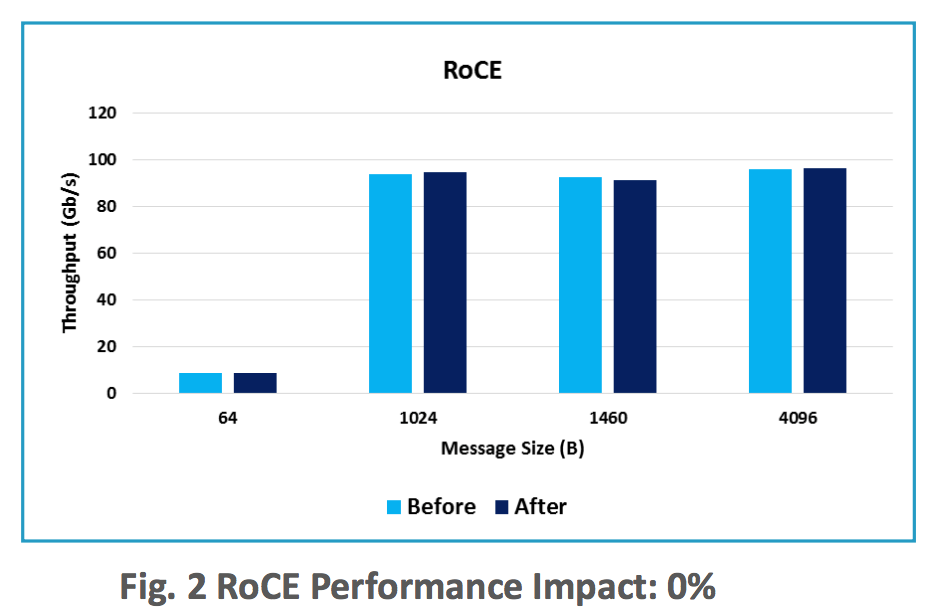
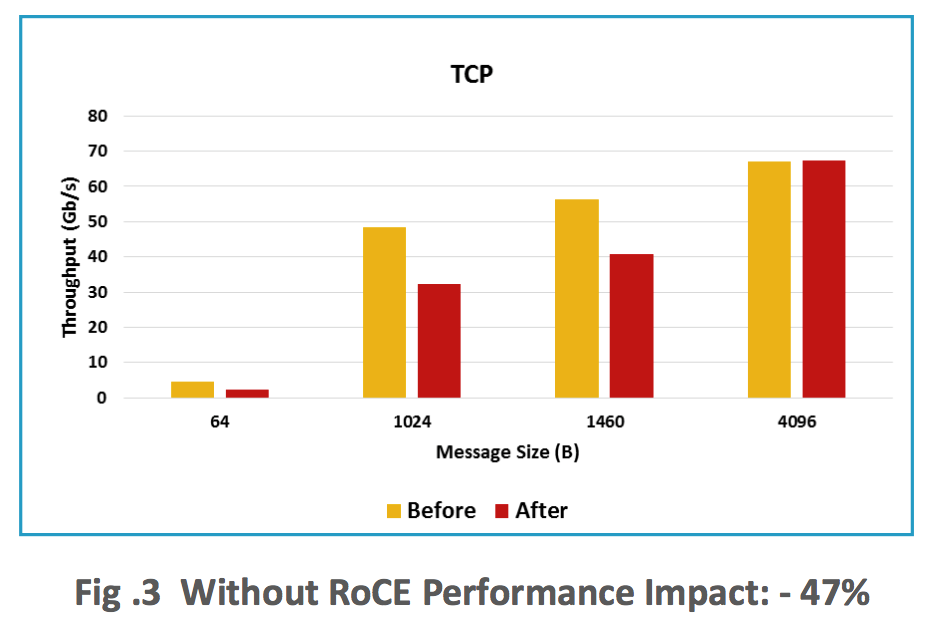
A solution, put forward by Mellanox in the form of SmartNICs avoids the performance degradation associated with the patches.
Mellanox say: “By deploying SmartNIC technologies that offload transport and memory protection processing from the CPU performance degradation can be avoided. Leveraging these offloads the SmartNIC shoulders the burden of processing the TCP/IP data processing and storage network stacks. Mellanox delivers offload technologies such as RDMA and DPDK to remove the burden of processing the TCP/IP and storage stacks from the main system processor, moving it to the network adapter.”
Boston presents a more compelling case than ever to utilise server offload technologies that are available with Mellanox network adapters and switches.
If you assume a 40 percent reduction in CPU cycles based on Meltdown, our customers would have to effectively double their hardware footprint. A customer running 50 servers today would need to account for 80 to 100 servers, at a cost of between $1 million to $3.5 million to compensate for the application workload hit that would come with implementing the patch. As a result, we are aware that customers have put a freeze on implementing the patch because they simply don't have the capital budget to acquire the hardware in order to implement it.
Alternatively; customers could invest in 60 dual port 100GbE NICs, with an estimated cost of $50k, to alleviate the performance impact without having to double their hardware footprint!
In summary, the reported workload performance degradation as a result of the Spectre and Meltdown security patches is going to have a huge impact on large data centers in both OpEx and CapEx, as servers will need to be replaced, or additional servers added to compensate for the performance losses. Mellanox ConnectX adapters with offload technologies will bypass the kernel and have a proven track record of accelerating performance.
Contact Boston today to discuss how Mellanox SmartNIC solutions such as ConnectX can mitigate the mess caused by Meltdown mess, and stop Spectre security slowdown.
For More:
https://www.mellanox.com/related-docs/presentations/2018/performance/Spectre-and-Meltdown-Performance.pdf?homepage-herobanner
https://www.boston.co.uk/blog/2018/01/08/intel-processor-security-statement-spectre-meltdown.aspx
https://www.supermicro.com/support/security_Intel-SA-00088.cfm
http://www.mellanox.com/blog/2018/02/spectre-meltdown-restore-security-performance-patches-mellanox-offload-technologies/